Table of Contents
UV EPROM erase
EPROM/EEPROM/flash can be erased by shining UV light or x-rays into the surrounding oxide. This slightly oxidizes it, letting the floating gate to drain out.
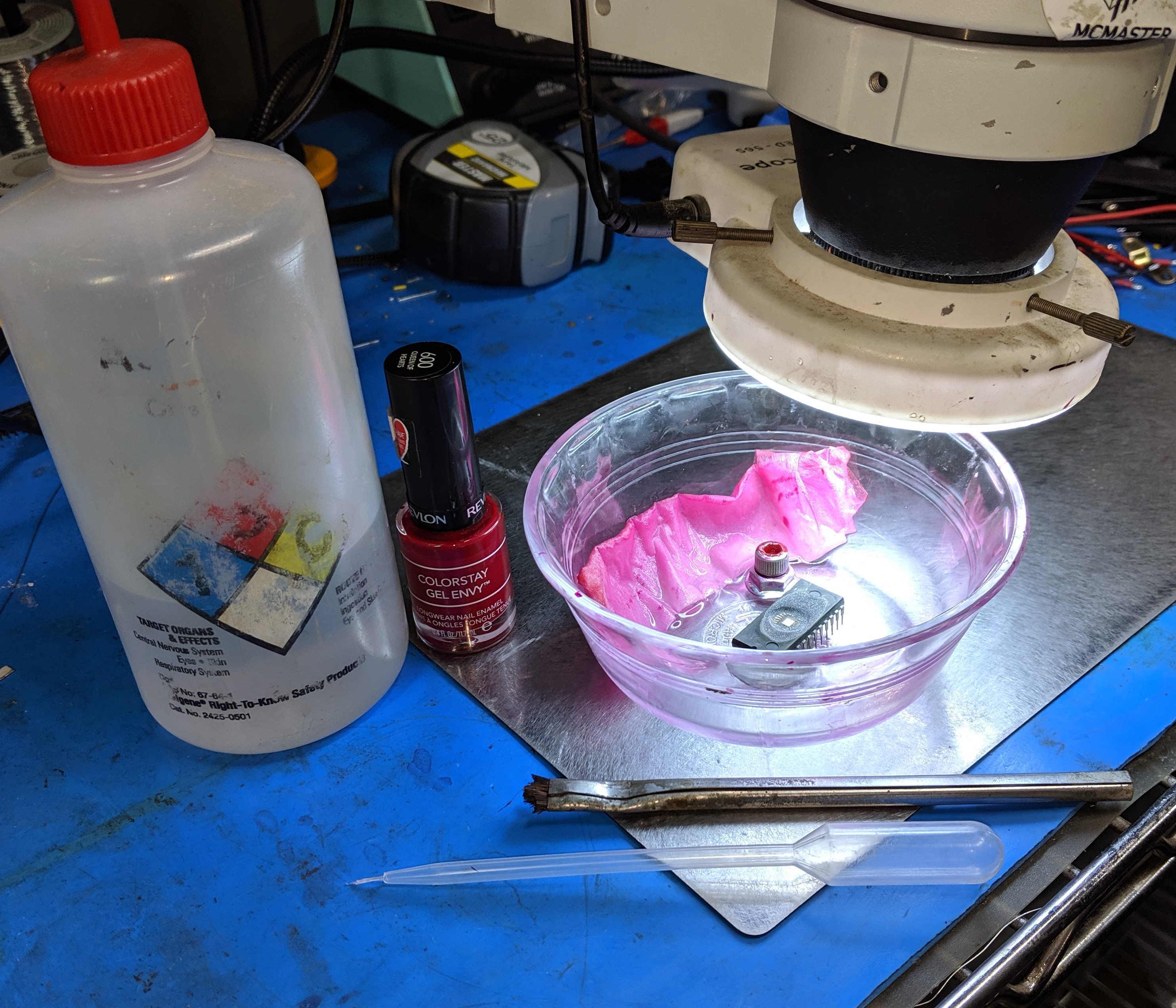
Usually a masking compound is applied to selectively block UV to the firmware, with red nail polish being the most popular or at least traditional.
McMaster misc notes
Application
- Use a single hair brush
- Ex: cut down MG 855-5 horse hair brush
- Place chip in bowl
- Shallow fill bowl with acetone
- Creates shield gas to prevent nail polish drying out in small quantities
- Place paper towel on side to elevate gas enough to keep nail polish liquid
- If nail polish is too viscous, slightly set top of chip with IPA
- Apply a glob of nail polish, then use the spring force of the liquid to precisely move it around
- By gently agitating the liquid boundaries its possible to very precisely move it forward
- Place the nail polish in the bowl in some sort of holder
- Ex: above image has a 1/4-20 SHCS with a nut screwed on as a base
Nail polish
- Also can be used to look fabulous!
- Bought at local store a while back and it seems to work well enough
- Other colors probably fine, but red is easy to see
Above: fine polypropylene tip for more aggressive cleaning. The tool is strong enough to damage bond wires though, so use sparingly
Nail polish removal
- Bulk removal with acetone, but leaves some residue around edges
- Remaining residue softened with acetone
- Remove using single hair brush if possible
- Can be more aggressive with PP monofilament wire
- Cold H2SO4 also works well. Wash with IPA then acetone
- Washing with water may really heat up the mixture
Angle
Some chips with shielding against this type of attack can be bypassed by shining light at a sharp angle
Mask
Use nail polish or similar compound. Most materials will block UV, so just about anything will work. Nail polish tends to be easy to work with including application and (acetone) removal.
Use a fine point pipette for simple chips.
For finer masks, place the chip in a large bowl with a shallow layer of acetone at the bottom. This creates an acetone “shield gas” to prevent tools from drying out. Then put some nail polish on a single bristle (maybe held by tweezers) and it should not dry out, allowing you to paint it onto the die.
X-ray EPROM erase
TODO: add links to misc papers
Violating design assumptions
Many systems have expectations that a piece of hardware will complete an operation in so long. For example, hardware may assume that an ADC will always complete within 100 ms. If evens are generated at 200 ms this normally might not be a problem. However, if one can find a way to stall the external hardware internal queues may overflow and result in unexpected states that can leak data or other vulnerabilities.